Your devs want MCP. Security wants to block it. You're stuck in the middle.
Golf governs every MCP connection - invisible to developers, visible to security. Your engineers keep every tool. Security gets full control. You stop being the bottleneck.
You've seen this before
Security blocked it
Engineering adopted Cursor and Claude Code. Productivity went up. Security filed a ticket. Now there's a meeting next Tuesday to "discuss AI tool policy." You know how this ends: a blanket ban, a spreadsheet of approved tools, and your best devs updating their LinkedIn.
You approved it with duct tape
You built a Notion database of approved MCP servers. Developers self-report what they connect. It's an honor system. You have no way to enforce read vs. write access, no way to know who's connecting to what, no way to prove anything to security.
Shadow MCP is already here
Developers didn't wait for approval. They spun up MCP servers for GitHub, Postgres, internal APIs. Connected them to Cursor and Claude Code. Running in production. You don't know how many exist because your tooling doesn't see MCP traffic.
The longer you wait, the harder it gets
You become the bottleneck
Every new AI tool needs your approval. Every approval needs security sign-off. Every sign-off takes months. Meanwhile your devs are waiting - or worse, not waiting.
Shadow AI wins
The reason you have shadow AI is because you're not moving fast enough. Every week without a governance path is another week developers route around you.
Someone else solves it
If platform eng doesn't own MCP governance, security will - with a blanket ban. Or nobody will, and you inherit the mess later.Career risk box: The question isn't whether your org adopts MCP. It's whether you enable it with governance - or clean up after it without.

Enforce. Discover. Audit.
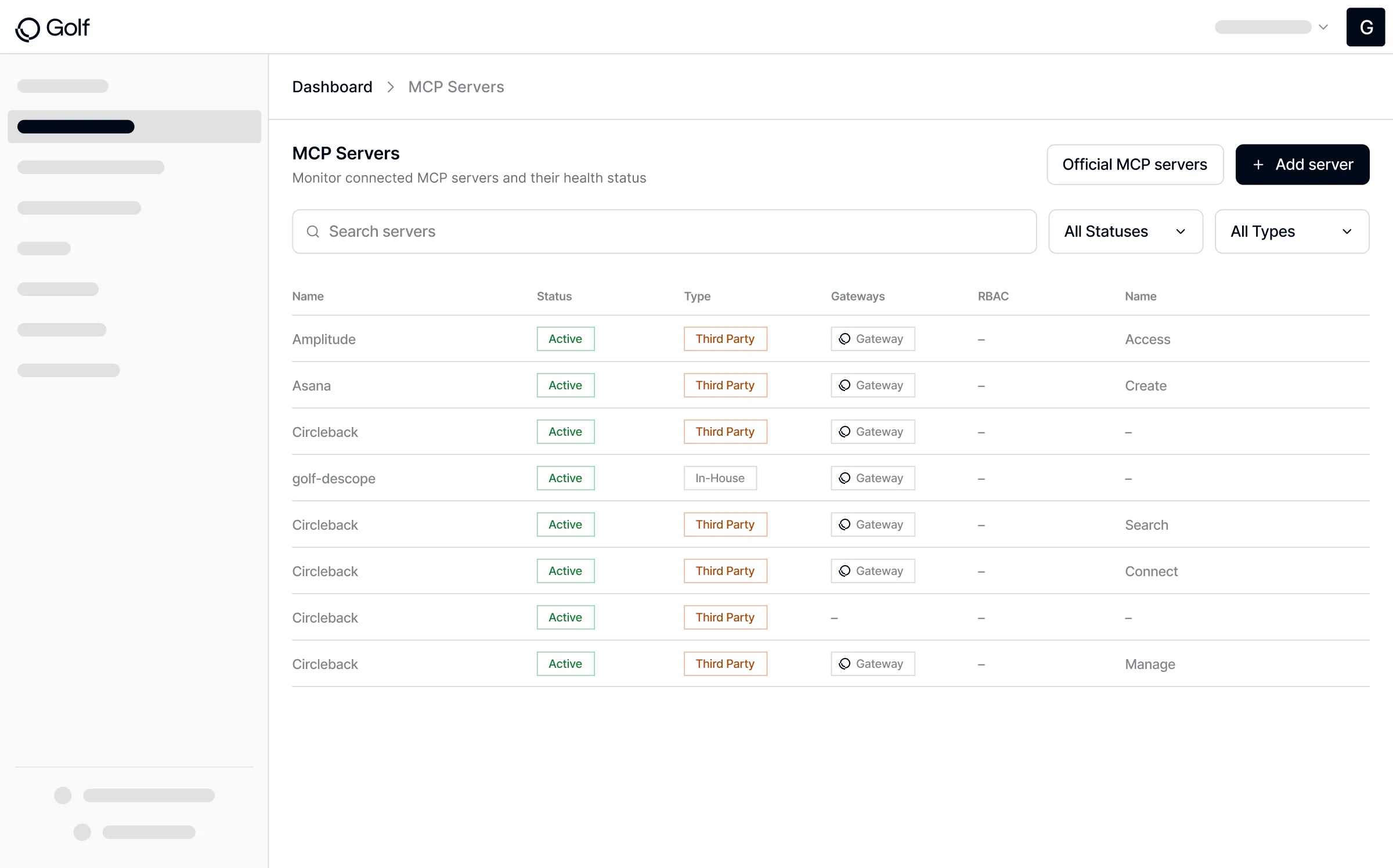
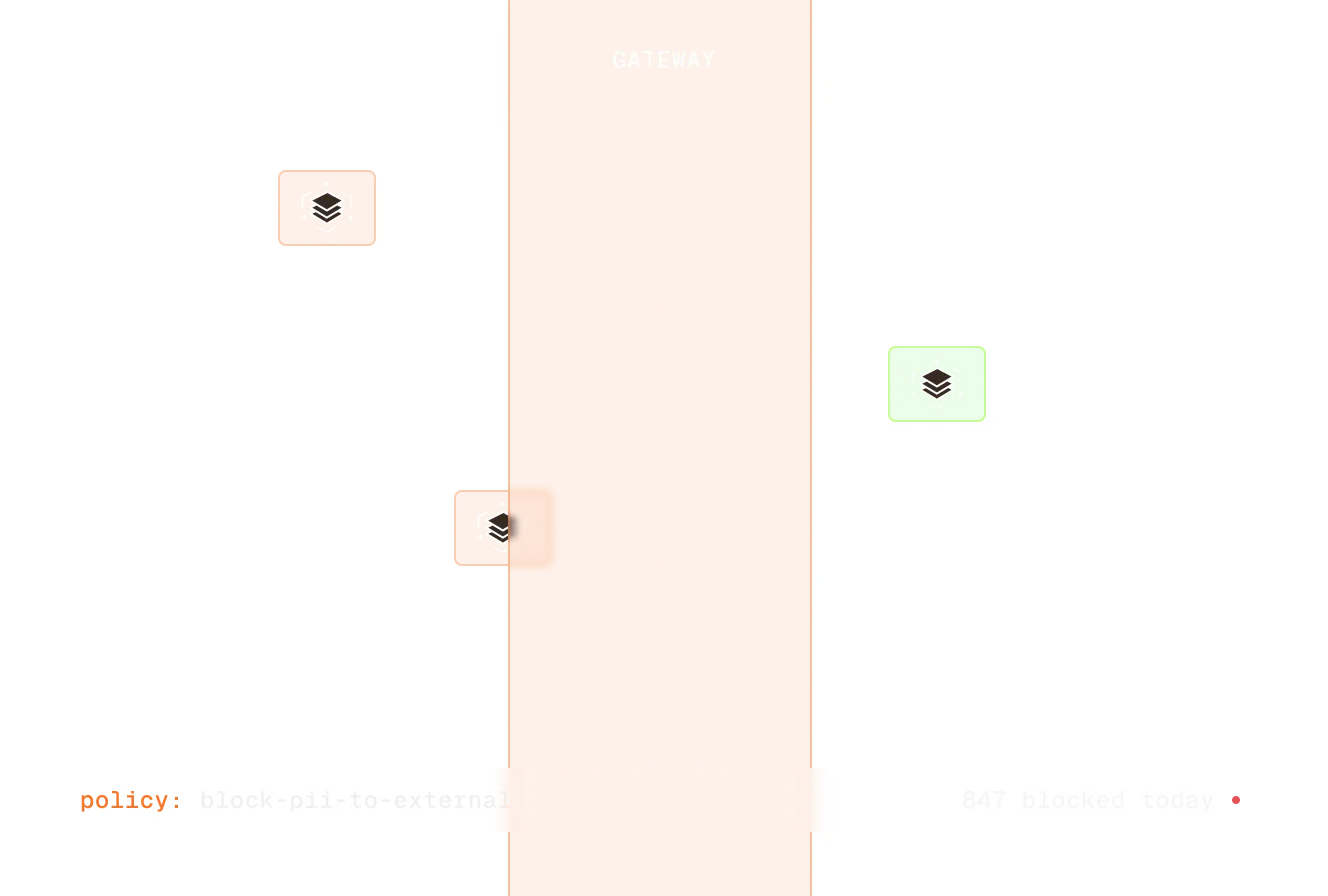
Golf sits at the MCP layer. Developers don't feel it. Security sees everything. You deploy it once and stop being in the middle.
Enforce
Set policies once, apply everywhere. Read vs. write per MCP server. Per team, per tool, per data source. Your devs keep Cursor, Claude Code, Copilot - security gets granular control. Nobody asks you to manually approve each connection.
Discover
See every MCP server running in your environment. No more Notion databases. No more honor system. Auto-discovered, auto-classified. You finally have the inventory security keeps asking for.

Audit
When compliance asks "what's connected and who authorized it?" - you have the answer in seconds. Full log of every connection. No more scrambling to build a spreadsheet before a review.

"Golf gave us governance for AI tools we don't control. That's the actual problem nobody else was solving."
— Head of AI, Enterprise Software Company
3 steps. Live in days.
Connect
Your identity provider and your SIEM. Golf maps your org and starts streaming logs.
Deploy
MCP Control Plane in your environment. On-prem, hybrid, or cloud. Data never leaves.
See everything
Every MCP server. Every agent. Every connection. Secured.
Enable MCP without becoming the bottleneck
Zero developer friction
Previous solutions: 17 onboarding steps per developer. Golf: 3 steps. No CLI changes, no IDE plugins, no workflow disruptions. Developers don't know it's there.
Governance ≠ blocking
Every other approach either blocks tools or ignores them. Golf is the third option - govern at the MCP layer, invisible to the people using the tools.
You own the catalog
No more Notion databases and honor systems. Golf auto-discovers every MCP server and gives you a real catalog - approved, pending, shadow - that security actually trusts.
Enable your engineers while keeping full control.
30-minute call. We'll show you how Golf governs every MCP connection without changing a single developer workflow.